Search results for: 'Find the Remainder when 31989 is divided by 7 (1) 2 (2) 6 (3) 4 (4) 5'
- Related search terms
- Find the domain of, where of f/g, where f(x) = x 9 and g(x) = x ^ 2
- (1)按索赔的依据进行分类,索赔可以分为( )。 A.工程加速索赔 B.工程变更索赔 C. 合同内的索赔D.道义索赔 E. 合同中明示的索赔
- the graph of two functions (f g)(2)
- The Epstein Files read like a modern-day nightmare. These files don't scream; they accuse. Once read, the question is no longer
- when genius failed free e book pdf
- Winsco Copper Voltameter$120.00
- Water Sampling Kit, Fieldmaster®$461.95
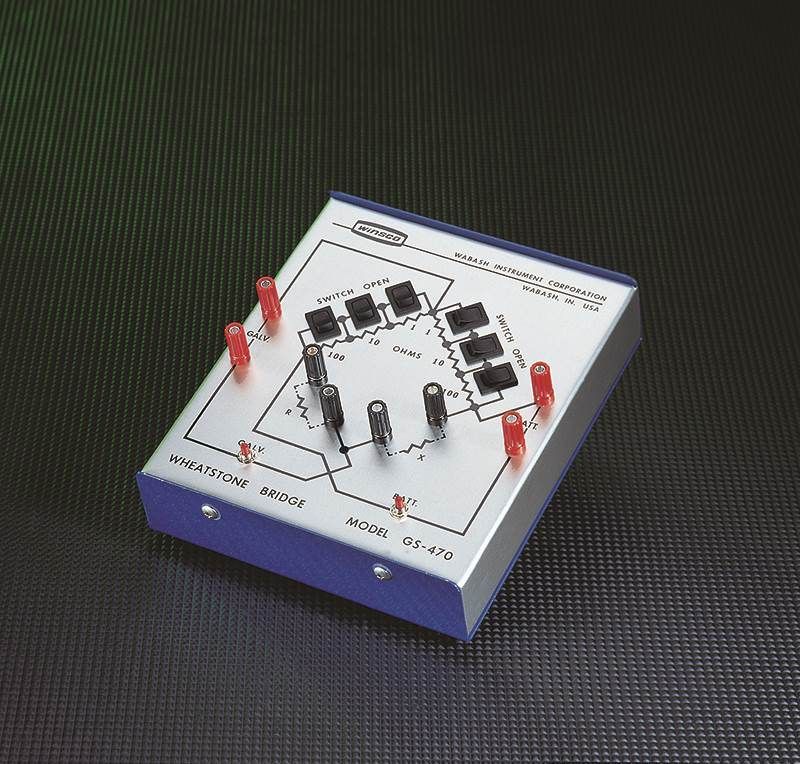
- Bridge, Wheatstone, Diamond Form$395.00
- Kalah Board Game With Beads$13.80
- Tower Of Hanoi Game$13.81
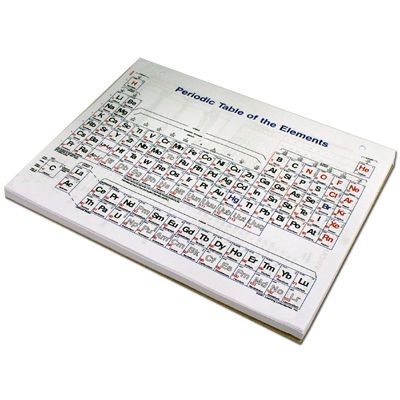
- Periodic Table Wall Chart.$69.25

 Biology
Biology Chemistry
Chemistry Earth Science
Earth Science Labware
Labware Physics
Physics Wildco Environmental Sampling
Wildco Environmental Sampling