Search results for: 'bloodstained ritual of the night 2'
- Related search terms
- The Microarchitectural Data Sampling (MDS) vulnerabilities are a set of weaknesses in Intel x86 microprocessors that use hyper-t
- The Guy She Was Interested In Wasn't A Guy At All N.2
- the plant shack e email address
- THE MUNICIPAL TRIAL COURT GRAVELY ERRED IN NOT FINDING THAT PLAINTIFFS-APPELLANTS ARE ENTITLED TO THE RESCISSION/RESOLUTION OF T
- The recipient's mailbox is full and can't accept messages now. Please try resending your message later, or contact the recipient
- Air Pump, Hand.$23.05
- Guinea and Feather Tube.$41.00
- Magdeburg Hemispheres.$31.76
- Boyles Law and Absolute Zero.$109.15
- Conductivity of Water Tester$35.61
- Heros Fountain.$46.15
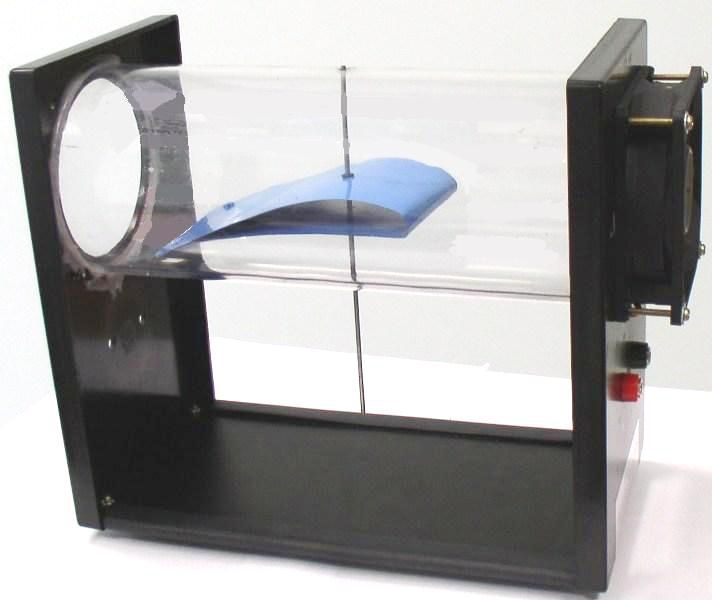
- Wind Tunnel$69.25

 Biology
Biology Chemistry
Chemistry Earth Science
Earth Science Labware
Labware Physics
Physics Wildco Environmental Sampling
Wildco Environmental Sampling