Search results for: 'the graph of two functions (f g)(2)'
- Related search terms
- The Microarchitectural Data Sampling (MDS) vulnerabilities are a set of weaknesses in Intel x86 microprocessors that use hyper-t
- the plant shack e email address
- The possibility of victory through science and technology, or the certainty of defeat by abandoning it. The Planet That Wasn't
- The observer's brain is very sensitive to ratios in images. Good makeup shifts the observed ratios to ranges the brain has been
- The recipient's mailbox is full and can't accept messages now. Please try resending your message later, or contact the recipient
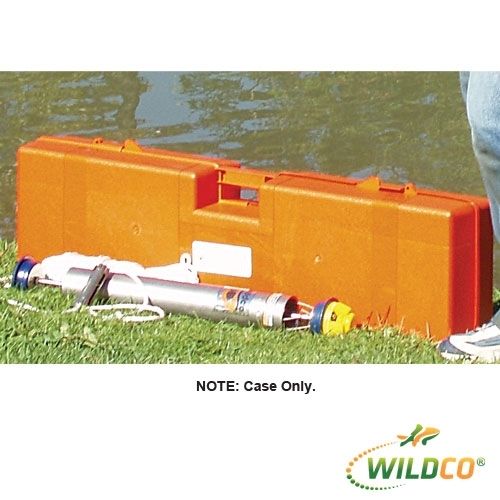
- Case, Plywood 12x13x15.25$215.18
- Case, Plywood 38W X 7.75D X 8H.$229.85
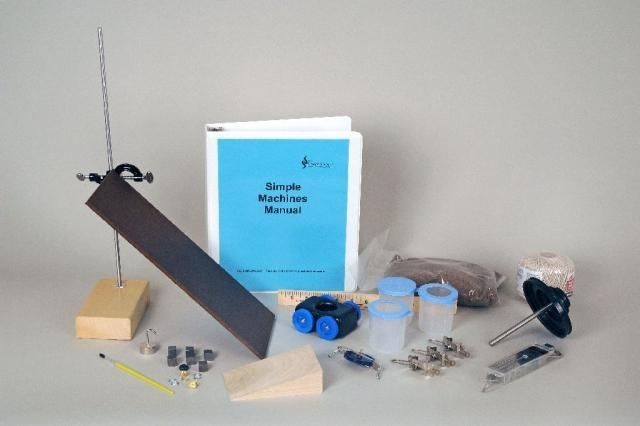
- Simple Machines, Elementary$209.81
- Simple Machines Kit, Deluxe$488.91
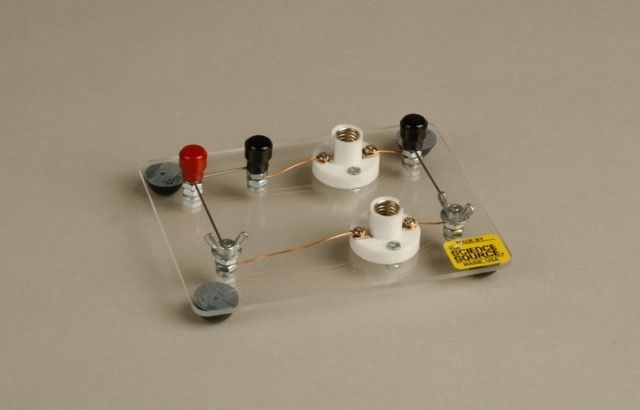
- Series Parallel Lampboard$31.76

 Biology
Biology Chemistry
Chemistry Earth Science
Earth Science Labware
Labware Physics
Physics Wildco Environmental Sampling
Wildco Environmental Sampling